Backup, Business Continuity & Disaster Recovery
Secure Your Business with Our Backup and Business Continuity Services
Backup, Business Continuity, and Disaster Recovery Services
We understand that data is the lifeline of your business. Our comprehensive suite of Backup, Business Continuity, and Disaster Recovery services are designed to ensure that your business remains resilient in the face of unforeseen events.
Why You Need Comprehensive Data Protection
In today’s fast-paced digital environment, your business’s data is constantly at risk from cyber-attacks, human error, hardware failures, and natural disasters. The loss of critical data can halt your business operations, leading to significant financial losses and damage to your brand reputation. That’s why implementing a robust data protection strategy is not just advisable; it’s essential.
82%
FIRST TOUCH RESOLUTION
97%
CUSTOMER SATISFACTION
60 Seconds
AVERAGE ANSWER TIME
Data Backup Solutions
Data Backup Solutions: Recognizing that every business has unique data needs and risks, we offer customized data backup solutions tailored to your specific requirements. Whether it’s cloud-based, on-premises, or hybrid systems, we ensure that your data is backed up efficiently, securely, and in compliance with industry standards. Our state-of-the-art encryption methods protect your data during transit and in storage, minimizing the risk of unauthorized access and ensuring that your information remains intact and confidential.
Business Continuity Planning: Our business continuity strategies go beyond mere data recovery. We focus on ensuring the continuity of your critical business operations in the face of disruptions. By conducting thorough risk assessments and business impact analyses, we identify your key business areas and processes and develop strategies to maintain operational integrity, no matter the circumstance. This proactive approach minimizes downtime and ensures that your business remains dynamic and responsive, even in the most challenging situations.
Disaster Recovery Services: Our disaster recovery services are built on the pillars of speed, efficiency, and adaptability. Understanding that time is of the essence during a crisis, we employ rapid response mechanisms to restore your systems and data with minimal delay. Our scalable solutions are designed to meet the needs of businesses of all sizes and sectors, ensuring that you can resume normal operations swiftly and smoothly following any disruption.
Regular Testing and Reporting: Regular testing is crucial to ensure that your backup and disaster recovery systems work when you need them most. We provide comprehensive testing and reporting services to validate the effectiveness of your data protection strategies, allowing for adjustments and improvements as needed.
Compliance and Security: In today’s regulatory environment, compliance is as crucial as security. Our services are designed to ensure that your data management practices meet all legal and regulatory requirements, safeguarding you from legal ramifications and reinforcing your business’s integrity. We stay abreast of the latest in compliance standards and cybersecurity threats, adapting our strategies to provide top-notch protection and peace of mind.
24/7 Monitoring and Support: We believe in offering more than just solutions; we provide unwavering support. Our experts are available 24/7 to monitor your systems, respond to incidents, and assist with any concerns. Our commitment to your business’s continuity and resilience is unwavering, and our support team is always ready to ensure that your operations run smoothly, securely, and without interruption.
Dissatisfied with Your Current IT Provider?
Switch to Verity IT for Simple, Stress-Free IT Solutions.
What Does Continuity Mean for Your Business?
Imagine you are a medical practice that can’t book appointments because your server is down or a law firm that needs specific case files, but those files were recently “locked-up” by ransomware — how will you stay in business? How will this impact your customer experience? Most importantly, how will this impact your revenue targets?
Now imagine getting all your data back within a matter of seconds. It’s no longer a matter of “if,” but “when” a real-world threat will compromise your business data. Between natural disasters, viruses, user error and ransomware, these threats are becoming ever-present.
Avoid Downtime With Verity IT’s Backup Solutions
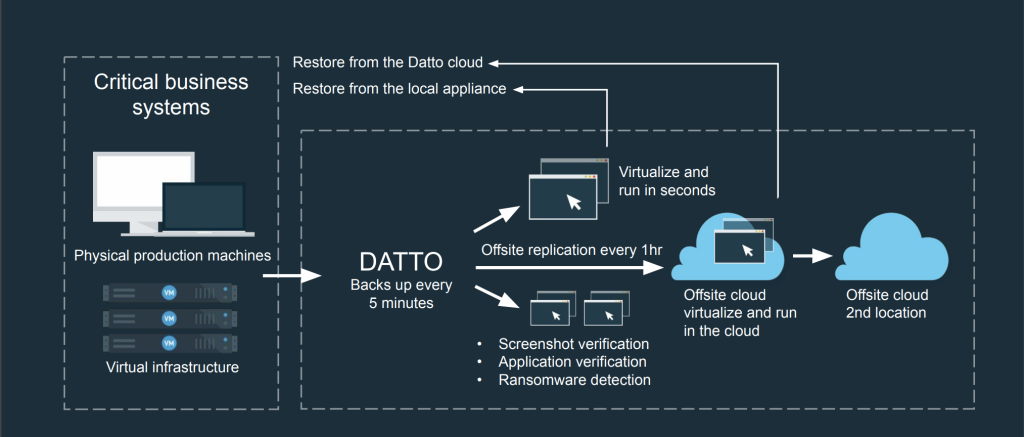
Hybrid-Cloud Based Backup & Disaster Recovery
In short, hybrid-cloud backup provides a combination of cloud data backup and storage with local backup. The cloud storage is integrated with the local backup to ensure your critical data is protected in the event of a disaster.
How it works:
Why Do You Need Hybrid-Cloud Backup?
More Recovery Options
Local and Cloud Backups
Reduces Downtime
Ransomware Detection
Backup for Microsoft 365 and Google Workspace
Microsoft 365 backup service includes features to safeguard and recover critical data within the Microsoft 365 environment. Some common features are:
Email Backup
Back up Exchange Online emails, attachments, and metadata to protect against accidental deletion, corruption, or cyber threats.
OneDrive Backup
Safeguard files and folders stored in OneDrive, ensuring data protection and recovery in case of data loss.
SharePoint Backup
Back up SharePoint Online sites, lists, libraries, and permissions to prevent data loss and facilitate recovery.
Calendar and Contacts Backup
Protect calendar events and contact information in Exchange Online.
Point-in-Time Recovery
Enable the restoration of data to a specific point in time, allowing users to recover from historical backups.
Granular Recovery
Provides the ability to restore individual files, emails, or other items without the need to restore an entire dataset.
Automated Backup Scheduling
Backup snapshots are retained for up to 1 year in the Cloud, following the schedule: 3X daily backups are retained for 30 days; Dailies are kept after 30 days; & Weeklies are kept after 90 days, then stored rolling, for up to 1 year, ensuring regular and consistent protection of Microsoft 365 data.
Security and Compliance
Ensures that backed-up data adheres to security standards and compliance requirements.
Implementing a Microsoft 365 backup service helps businesses mitigate risks associated with data loss, accidental deletions, and security threats within their Microsoft 365 environment.
Stay One Step Ahead Potential Disasters
Cloud Backup for PCs
Eliminate data loss and get your employees back up and running quickly with Cloud Backup for their PCs. This reliable, image-based, all-in-one BCDR solution provides backup direct to the Cloud, screenshot verification, and multiple layers of recovery capabilities including Bare Metal Restore, and File/Folder Recovery. In the event of a lost or stolen PC, ransomware attack, or other disaster, Verity IT can quickly and easily get your employee up and running, exactly as they had been before.
All-in-One BCDR for PCs
Whether it’s because of a ransomware attack, lost or stolen device, or accidental deletion of a file, Verity IT can assist with protection of endpoint business data on your Windows 7 and Windows 10 devices, but also for streamlined recovery of the entire device configuration, setup and applications.
- Recover individual files and folders
- Rollback from ransomware attacks
- Restore lost or stolen PCs
Reliable PC Backups
PCs move between networks or get powered off, making it difficult to get reliable backups. Cloud Backup for PCs backup automatically pauses when the device has its connection interrupted and then automatically resumes once the connection is restored. Integrity checks, like Screenshot Verification, validate every backup and provide an alert if there are any issues. This takes the guesswork out and ensures backups are good for a reliable recovery.
For one simple price it protects the primary OS volume of an endpoint device up to 1 TB in size. Backups are available with 1-year time-based retention (TBR) in the Cloud.
Key Features
- Image-based Cloud BCDR
- Automatic backup pause and resume
- Screenshot Verification
- File Restore
- Bare Metal Restore (BMR)
- No additional appliance required
- No storage management required
- One price, no additional fees
Operating System and Hardware Compatibility
- Supports Windows 10 (64-bit) and Windows 7 (64-bit)
- Requires 1 GB of free RAM on protected device
- Protects the primary OS volume (single-volume) up to 1 TB in size
e-book: Backup & Data Protection for Growing Businesses
What You Need to Know About Keeping Business-Critical Data Accessible
Why Partner With Verity IT for Your Backup and Disaster Recovery?
Verity IT goes beyond traditional backup to deliver business continuity and disaster recovery solutions to our clients. Our solutions provide cross-platform server, application and virtual machine data protection to ensure your business can continue to operate through an event. We ensure:
- Your organization will have access to its data when needed.
- Complete backups — not just files — for total data recovery.
- Fast backups that cause zero disruption to your day-to-day business.
- Immediate backup restoration that minimizes downtime after a disaster.
- Hourly backups — keeping your most recent data is safe.
- Replication to the cloud to protect your data from natural disasters, fire and theft.
Our proactive solutions provide complete business continuity, protecting business networks of all sizes.
Ready to Get Started with Managed Backup Services?


