Onboarding
Dark Web Monitoring
Our Dark Web Monitoring Service helps protect your business from data breaches due to compromised employee credentials by monitoring the Dark Web in real time and automatically alerting you when it’s time to change passwords because your credentials are up for sale on the Dark Web. Dark Web Monitoring is a must have in cybersecurity protection for businesses.
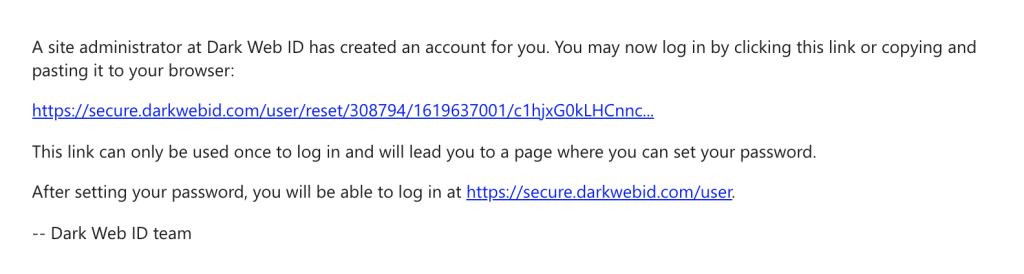
Within 72 hours, an automated email will be sent to the email address provided to your Sales Rep. This email will come from Dark Web ID <[email protected]>.
The email will contain instructions for logging into your Dark Web Monitoring Account. Here you will be able to view items such as: your Dashboard, Compromises and Reporting.
The email will look similar to the below screenshot:
You will be notified via email if and when your data has been compromised on the Dark Web. Here is an example of what the email will look like:
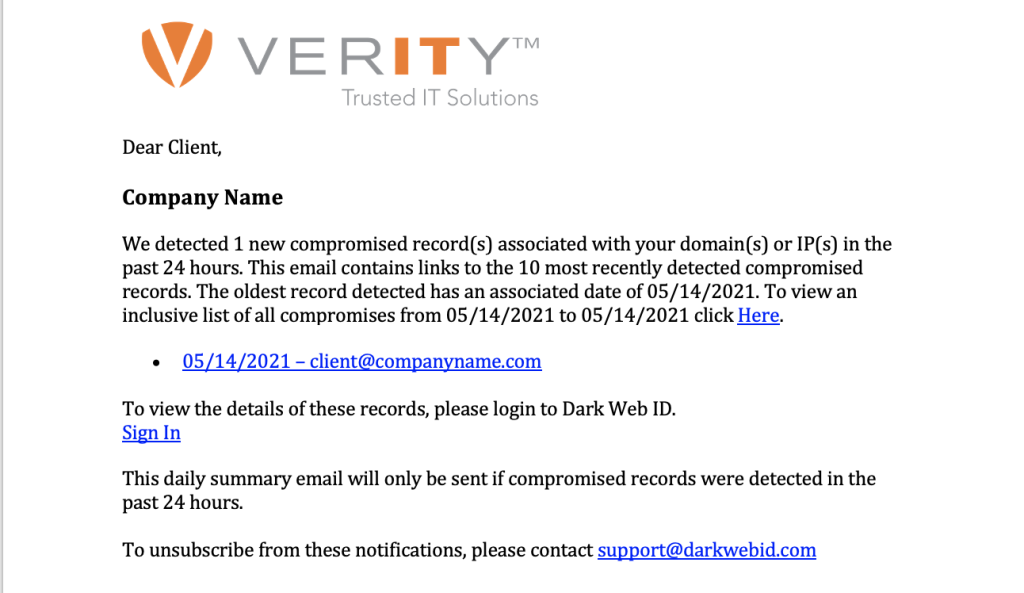
You will receive a “clean bill of health email” if no compromises are found.
It is the client’s responsibility to view and remediate any findings within the Dark Web Portal. Remember, we are monitoring for 3rd party breaches containing your information. If the password contained in the report is indeed yours, remediation is often as simple as changing your password.
Our service is designed to help businesses like yours detect and mitigate cyber threats that leverage stolen email addresses and passwords. We leverage a combination of human and artificial intelligence that scours botnets, criminal chat rooms, blogs, websites and bulletin boards, peer to peer networks, forums, private networks and other black-market sites 24/7, 365 days a year to identify stolen credentials and other personally identifiable information (PII).
The “Dashboard” tab or Cyber Threat Overview provides a graphical representation of your business’s compromises. This will be the first screen you encounter.
Two infographic types will be displayed depending on whether compromise(s) have been detected. If Domains, IPs, and/or emails have been monitored and no compromises have been reported, a blue checkmark will be displayed. If there has been at least one detected compromise, a pie chart will be displayed.
No reports will be sent, as you will have direct access to the Dark Web Monitoring Portal, where you can access your account activity in real time.
You will receive an email daily if and when one of your credentials is compromised on the Dark Web. Otherwise, you will receive a “clean bill of health” email on a monthly basis.
Security Awareness Training
90% of security breaches are inadvertent, unintentional and caused by human error. Security Awareness Training empowers your employees with the knowledge and skills to stay cybersecure at work and at home. With hundreds of awareness and training resources and phishing simulations, you’ll have everything you need to prepare employees to detect, report and defeat cybercrime.
Congratulations on making the choice to protect your business with Security Awareness Training!
In order to get started, please complete and return the Learner List Template to [email protected]. When your completed template is received, we will begin to build out your 12-Month Security Awareness Training Program!
Yes. You will receive an email from your Verity IT Sales Account Executive prompting you to complete a template of learners. Once this is completed and sent back, someone from your company will need to make sure to whitelist sending IPs, domains and header information for phishing simulator.
Verity IT will upload all your learners, schedule the training and phishing simulations and will provide quarterly reports.
Verity IT will provide reports on a quarterly basis.
